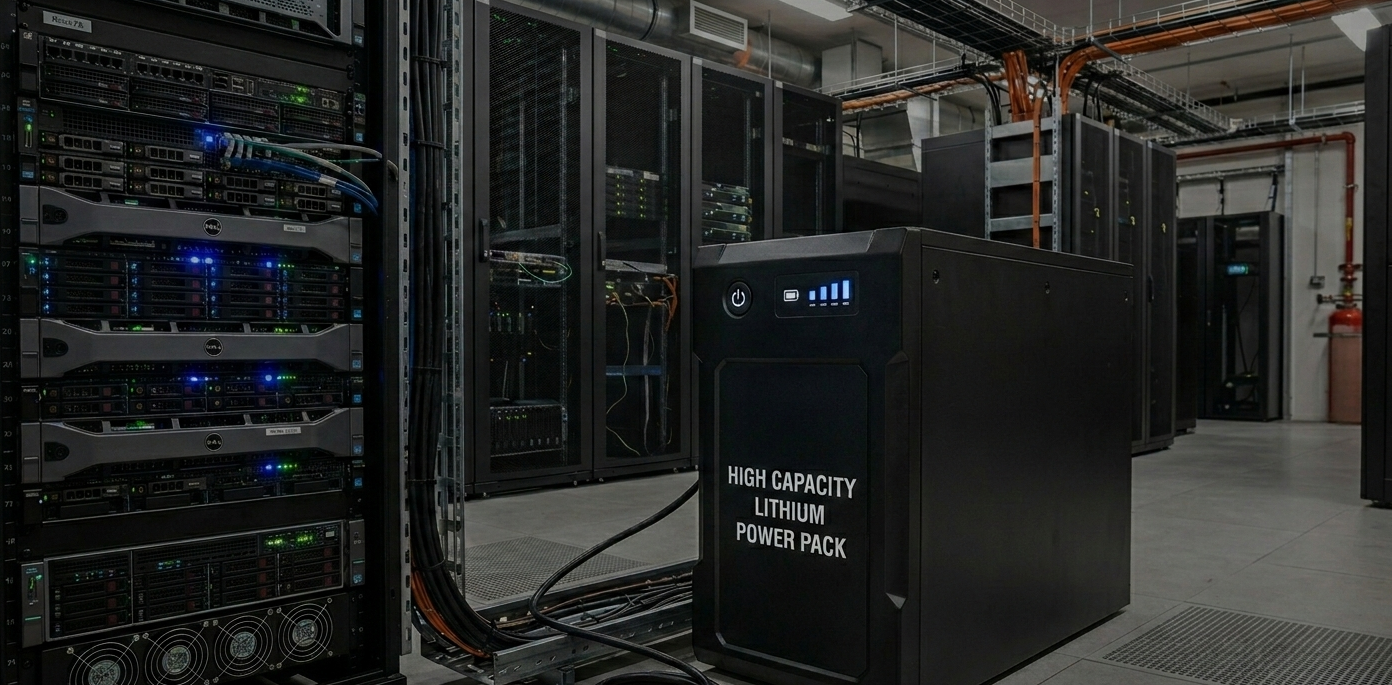
Power as a Service. Everything within UPS for your company
Our service is ideal for businesses that want to ensure a stable and reliable power supply without having to manage the complexity themselves. Contact us to discuss how we can help you find the best solution for your business.
With our Power as a Service, we offer a complete solution for your power supply, from correct sizing to installation, configuration and monitoring. We ensure that you always have the right UPS (Uninterruptible Power Supply) for your business needs.
Benefits of Power as a Service:
Simplicity: A complete solution with a single point of contact for everything related to your power supply.
Security: Continuous monitoring and professional service minimize the risk of unplanned downtime.
Cost control: You spread the cost over time and get full control over your expenses.
Expertise: You get access to specialists in both UPS systems and electrical installations
What is included in the service?
✓ Advice and sizing: We help you choose the right UPS model that is perfectly suited to your equipment and your specific power needs. We make sure that you neither over- nor under-size your solution.
✓ Installation and configuration: Our team handles the entire installation process. We install all hardware and configure the system correctly to ensure optimal performance and reliability.
✓ Monitoring: We monitor your UPS system in real time to quickly detect any problems. In the event of deviations, we act proactively to minimize the risk of downtime.
✓ Add on services -Electrician on demand: Should there be a need for electrical installations or other electrical work, we have certified electricians who can quickly be on site to help.