We already have an IT provider; why do we need this?
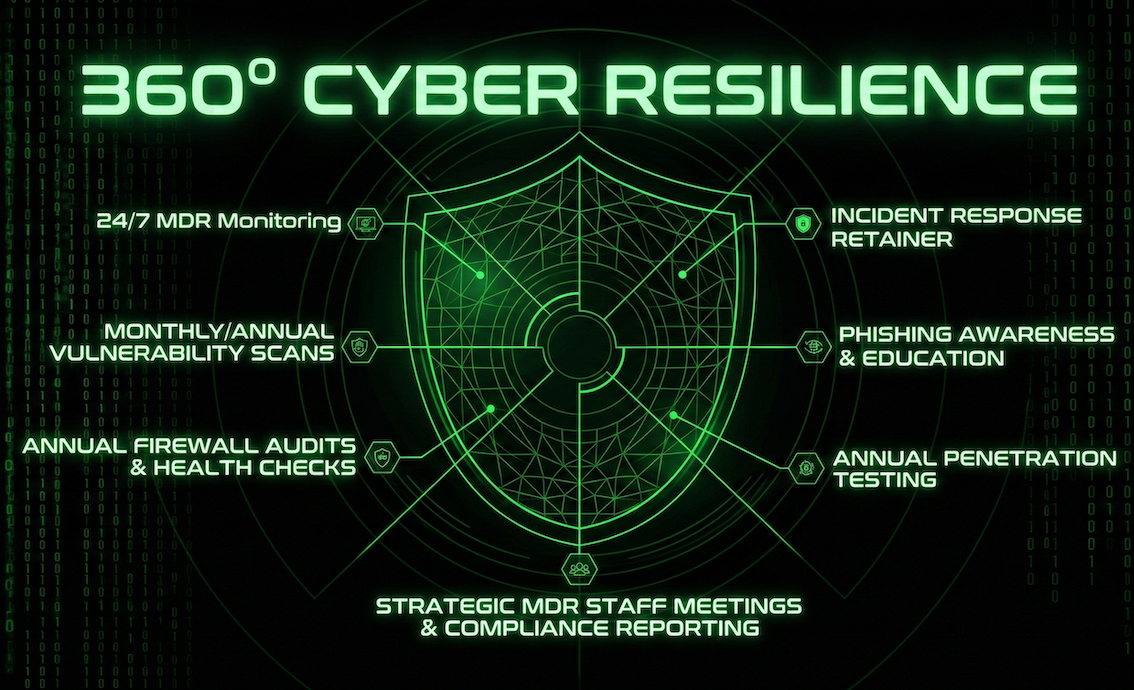
Your IT team keeps your systems running; we keep them secure. In 2026, cybersecurity requires specialized 24/7 monitoring (SOC) and deep audits that go beyond standard IT maintenance. We act as a specialized layer of defense that supports your existing team.